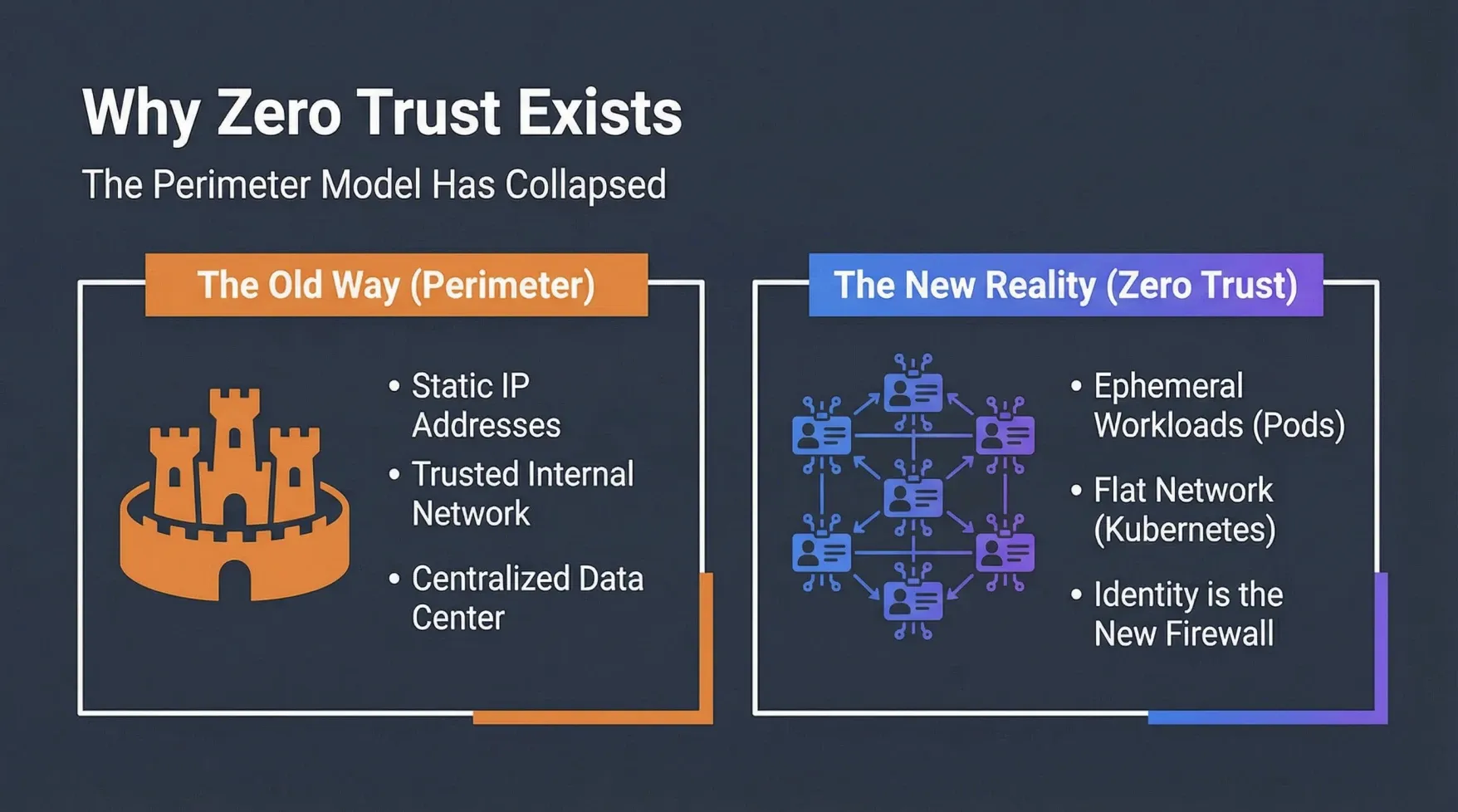
In the era of monolithic applications and on-premise data centers, security strategies often revolved around a perimeter-based model. This approach, frequently likened to a castle-and-moat defense, assumed that everything inside the network was trustworthy, while anything outside was inherently hostile. Firewalls and intrusion detection systems guarded the network’s edge, creating a hard shell around a soft interior.
However, the advent of cloud-native architectures, microservices, and container orchestration platforms like Amazon Elastic Kubernetes Service (EKS) has fundamentally reshaped the threat landscape. In these dynamic environments, the traditional perimeter has dissolved. Workloads are ephemeral, with pods constantly being created, scaled, and terminated, leading to ever-changing IP addresses. The network within Kubernetes is often flat, meaning pods can communicate freely by default, blurring the lines between trusted and untrusted zones. In this new reality, identity is the new firewall, and a new security paradigm is required: Zero Trust.
Why the Perimeter Model Fails in EKS
The shift to Kubernetes introduces several challenges that render the traditional perimeter model ineffective:
- Flat Network: By default, Kubernetes allows any pod to communicate with any other pod. This open communication model, while flexible, creates a vast attack surface if not properly secured.
- Ephemeral IPs: Pods are assigned dynamic IP addresses that change frequently. Relying on static IP-based firewall rules becomes impractical and brittle.
- Shared Kernel: All containers on a node share the same underlying operating system kernel. A compromise in one container could potentially impact others on the same node, increasing the blast radius.
- Complex Configuration: Securing Kubernetes often involves intricate YAML configurations for various resources, increasing the risk of misconfigurations that can lead to security vulnerabilities.
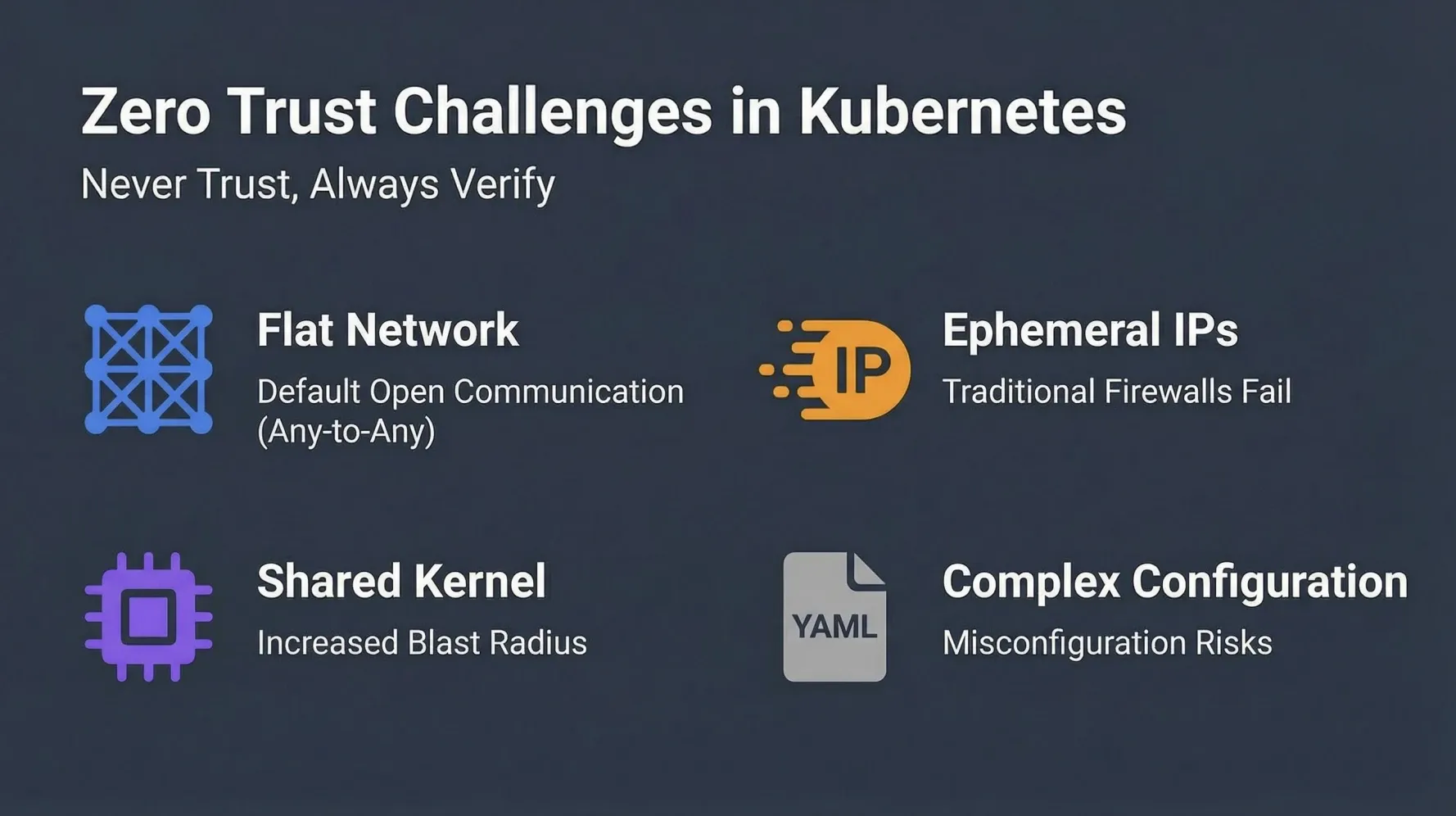
These challenges necessitate a security approach that doesn’t implicitly trust any entity, regardless of its network location. This is the core tenet of Zero Trust.
Introduction to Zero Trust: Never Trust, Always Verify
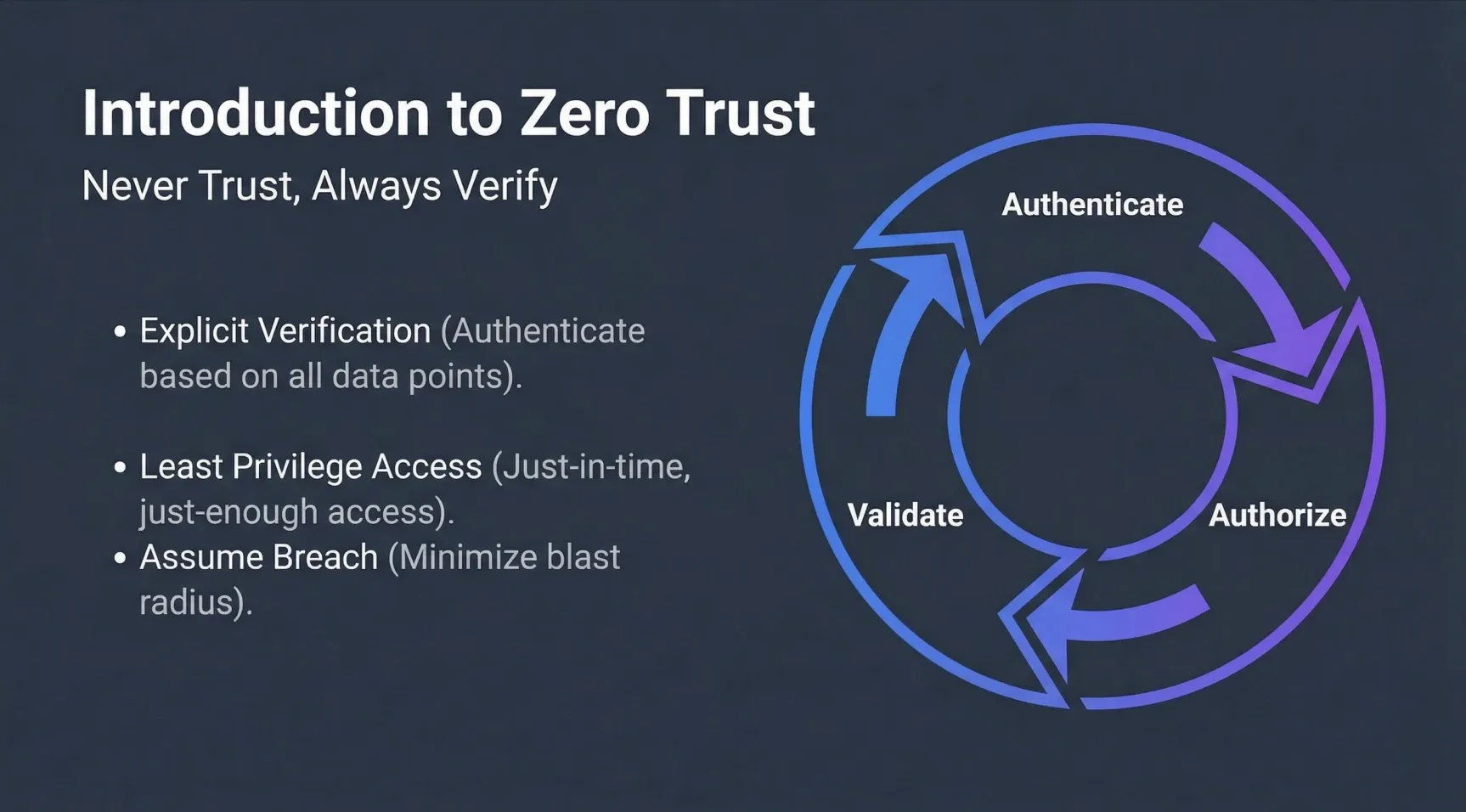
Zero Trust is a strategic cybersecurity model that operates on the principle of “Never Trust, Always Verify.” It mandates that every user, device, application, and workload attempting to access resources must be authenticated, authorized, and continuously validated before being granted access, and access should be limited to the absolute minimum required.
The foundational principles of Zero Trust include:
- Explicit Verification: All access requests must be explicitly verified based on all available data points, including user identity, device posture, location, service being accessed, and data sensitivity. This moves beyond simple network location as a trust indicator.
- Least Privilege Access: Access is granted on a “need-to-know” and “least-privilege” basis. This often involves Just-In-Time (JIT) and Just-Enough-Access (JEA) principles, ensuring that entities only have the permissions necessary for their current task and for a limited duration.
- Assume Breach: Organizations must operate under the assumption that a breach is inevitable or has already occurred. This mindset drives the design of security controls that minimize the “blast radius” of a compromise and prevent lateral movement within the network.
The Five Core Pillars of Zero Trust in EKS
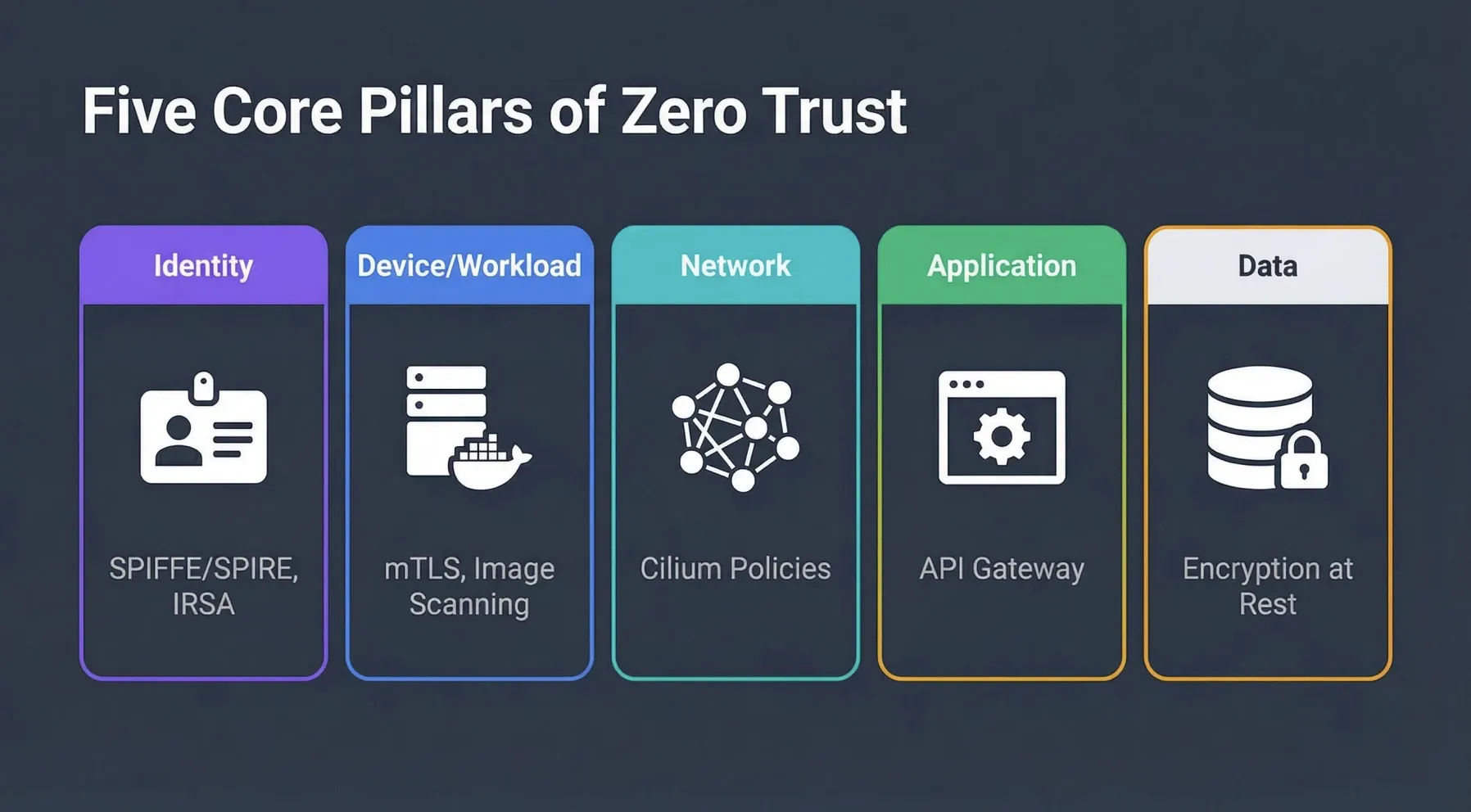
Implementing Zero Trust in an EKS environment requires a holistic approach, addressing security across multiple dimensions. The following five pillars provide a comprehensive framework:
| Pillar | Focus Area | Relevance in EKS | Example Implementation |
|---|---|---|---|
| Identity | Verifying the identity of users and workloads. | Critical for authenticating pods, service accounts, and human users accessing the cluster or applications. | SPIFFE/SPIRE for workload identity, AWS IRSA for cloud identity, IAM for user identity. |
| Device/Workload | Ensuring the security posture of devices and containerized workloads. | Securing container images, runtime protection, and ensuring only authorized workloads run. | mTLS between services, Image Scanning (e.g., Trivy, Clair), Admission Controllers (e.g., Kyverno, OPA). |
| Network | Micro-segmentation and secure communication channels. | Isolating pods and namespaces, encrypting traffic, and controlling ingress/egress. | Kubernetes Network Policies (e.g., AWS VPC CNI, Cilium), mTLS for encrypted communication. |
| Application | Securing applications and APIs. | Protecting APIs from unauthorized access, ensuring secure coding practices, and runtime application self-protection. | API Gateway security, Web Application Firewalls (WAF), secure API design. |
| Data | Protecting sensitive data at rest and in transit. | Encrypting secrets, databases, and storage volumes. | AWS KMS Envelope Encryption for Kubernetes Secrets, AWS Secrets Manager for dynamic credentials, database encryption. |
Defense in Depth: A Layered Security Model
Our Zero Trust EKS Demo exemplifies a defense-in-depth strategy, where multiple security layers are implemented to provide comprehensive protection. This layered approach ensures that even if one control fails, others are in place to prevent or mitigate a breach.
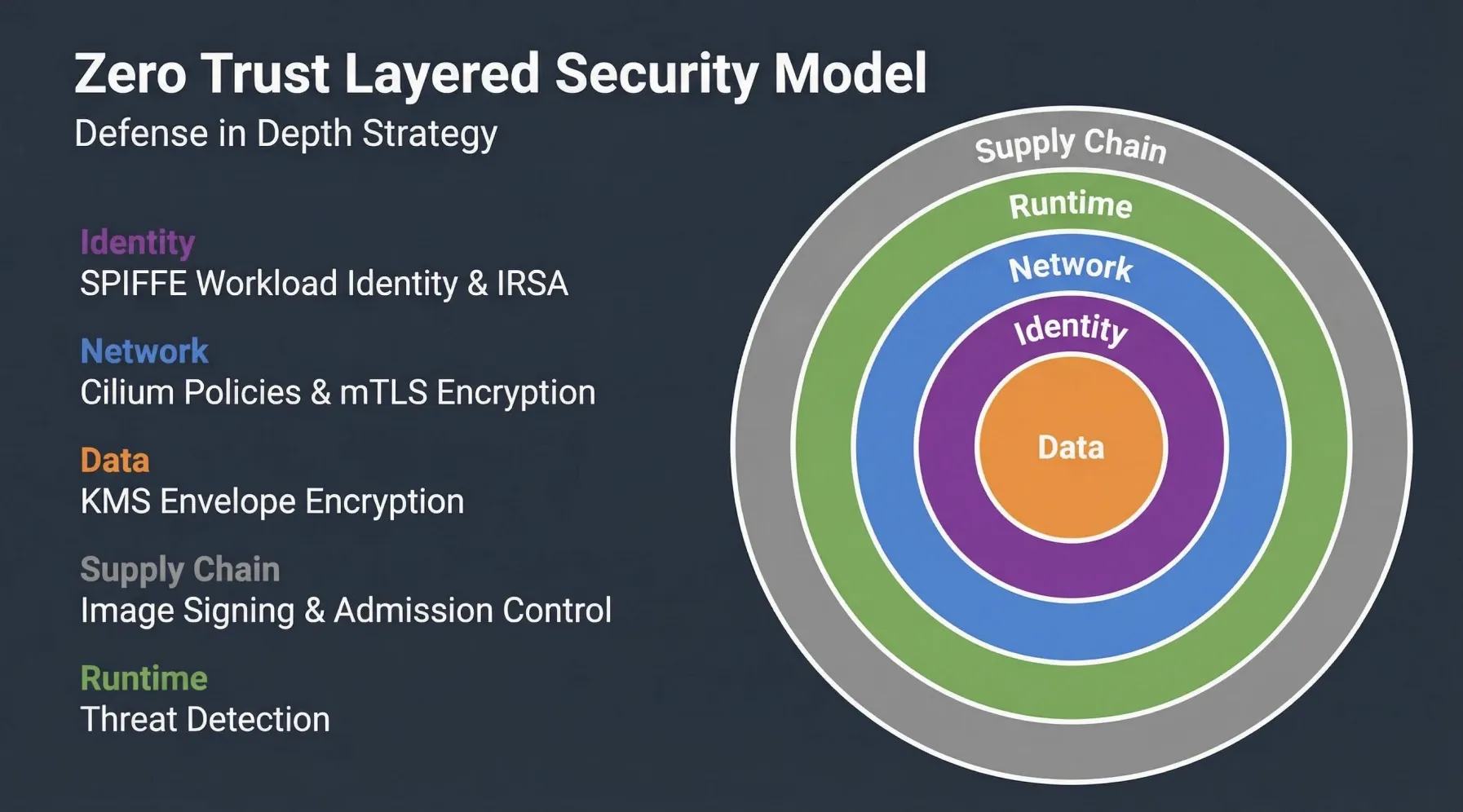
- Identity Layer (L7): Utilizing SPIFFE/SPIRE to assign cryptographically verifiable identities to workloads, enabling mutual TLS (mTLS) for secure service-to-service communication.
- Network Layer (L3/L4): Implementing a “Default Deny” posture with Kubernetes Network Policies to strictly control traffic flow between pods and namespaces.
- Cloud Identity Layer: Leveraging AWS IRSA (IAM Roles for Service Accounts) to grant fine-grained, least-privilege access to AWS resources for specific Kubernetes service accounts.
- Data Protection Layer: Employing AWS KMS for envelope encryption of Kubernetes secrets and AWS Secrets Manager for dynamic management of database credentials.
- Supply Chain Security: Ensuring the integrity of container images through scanning, signing, and admission control.
This multi-faceted approach significantly enhances the security posture of applications deployed on EKS. In the next post of this series, we will dive deep into the Identity Foundation and explore how SPIFFE/SPIRE replaces traditional IP-based trust with robust cryptographic identities for East-West traffic within your EKS cluster.
Stay tuned for a deeper dive into the technical implementations! If you have any initial thoughts or questions on the Zero Trust philosophy in EKS, feel free to share them in the comments below.